In today’s digital age, data has become one of the most valuable assets for individuals and organizations alike. However, with the increasing reliance on technology and the proliferation of cyber threats, safeguarding data has never been more critical. Data breaches and cyberattacks can lead to devastating consequences, including financial losses, reputational damage, and legal liabilities. To mitigate these risks, it is imperative to adopt robust data security measures. In this article, we will explore the 10 top data security best practices that can help protect your sensitive information.
1. Data Encryption
Data encryption is a fundamental security practice that involves converting sensitive information into an unreadable format using encryption algorithms. Only authorized individuals with the decryption key can access and understand the data. Employ encryption for data both in transit and at rest. Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols are examples of encryption methods for data in transit, while BitLocker and FileVault are tools for encrypting data at rest.
2. Access Control

Implement strict access controls to ensure that only authorized users can access sensitive data. Use role-based access control (RBAC) mechanisms to assign permissions based on job roles and responsibilities. Regularly review and update access permissions to match the current needs of individuals within your organization. This helps minimize the risk of unauthorized access or data leaks.
3. Regular Software Updates and Patch Management

Outdated software and unpatched systems are often vulnerable to known security flaws. Cybercriminals exploit these vulnerabilities to gain access to your data. To mitigate this risk, establish a robust patch management process to ensure that all software, operating systems, and applications are regularly updated with the latest security patches and updates.
Visit: blockchain trends to follow
4. Employee Training and Awareness

The weakest link in any data security system can often be human error. Therefore, comprehensive employee training and awareness programs are essential. Ensure that all employees understand the importance of data security, can recognize phishing attempts, and know how to handle sensitive data properly. Regular training sessions and simulated security incidents can help reinforce these practices.
5. Data Backup and Disaster Recovery Plans

Data loss can occur due to various reasons, including hardware failures, natural disasters, or cyberattacks. Implement a robust data backup strategy that includes regular backups and offsite storage. Additionally, develop and test a disaster recovery plan to ensure that your organization can recover data and operations in the event of a catastrophic incident.
Visit: how to invest in Web3
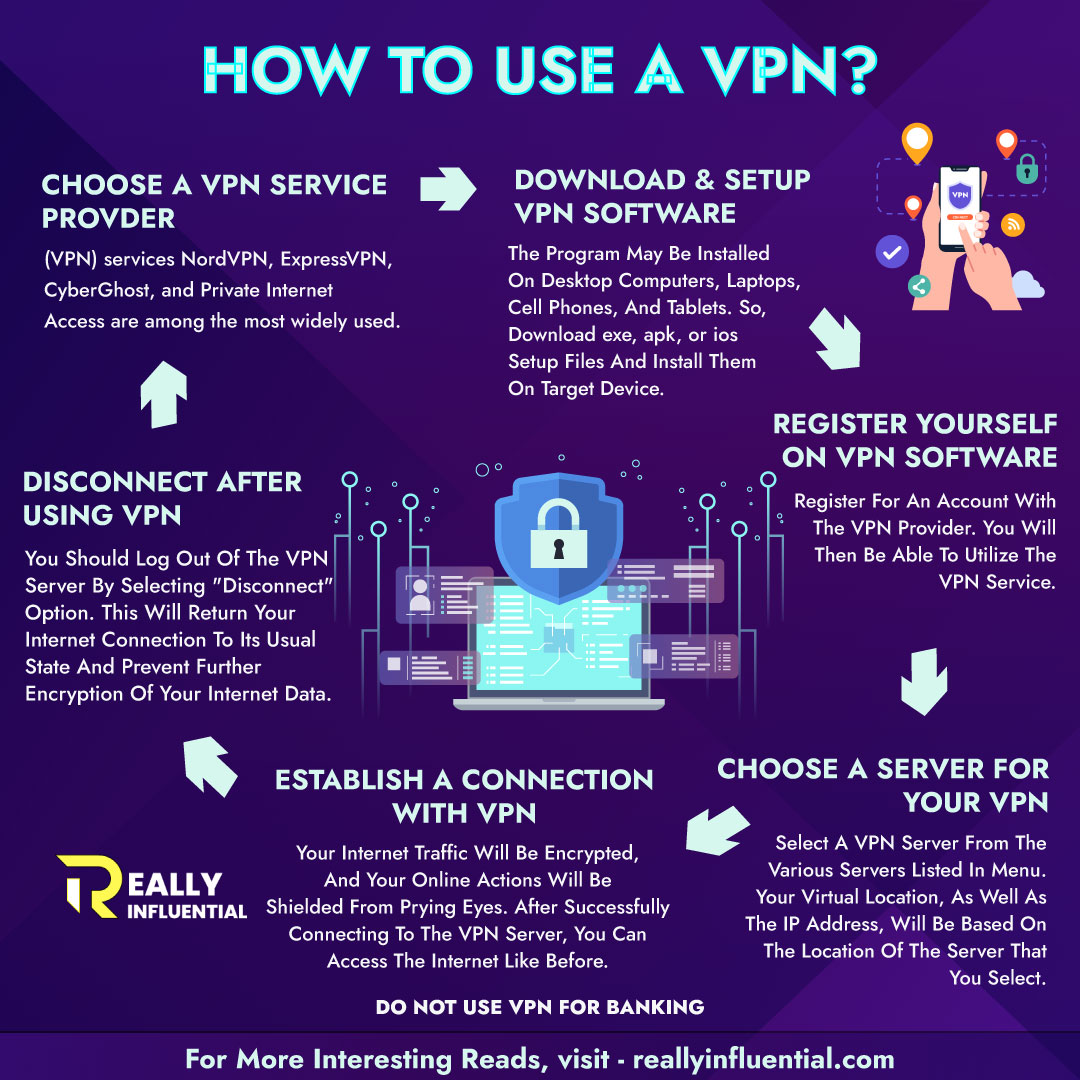
6. Network Security Measures

Protect your network infrastructure with firewalls, intrusion detection systems (IDS), and intrusion prevention systems (IPS). Segment your network to isolate sensitive data from less secure areas. Regularly monitor network traffic for suspicious activities and establish incident response procedures to address potential breaches promptly.
7. Multi-Factor Authentication (MFA)

MFA adds an extra layer of security by requiring users to provide multiple forms of authentication before granting access. This typically involves something the user knows (e.g., a password), something the user has (e.g., a mobile device), and something the user is (e.g., biometric data like fingerprints or facial recognition). MFA can significantly reduce the risk of unauthorized access, even if passwords are compromised.
8. Vendor Security Assessment

If your organization relies on third-party vendors for services or software, it’s crucial to assess their security practices. Ensure that your vendors meet your data security standards and adhere to industry-specific regulations. Contractually require vendors to comply with your data security requirements and undergo regular security assessments.
9. Incident Response Plan

No security system is foolproof, so it’s essential to have a well-documented incident response plan in place. This plan should outline the steps to take in case of a data breach or security incident. It should include procedures for containment, investigation, notification, and recovery. Regularly review and update the plan to adapt to evolving threats.
10. Compliance with Regulations

Depending on your industry and location, there may be specific data security regulations and compliance requirements that you must adhere to. Familiarize yourself with these regulations, such as the General Data Protection Regulation (GDPR), the Health Insurance Portability and Accountability Act (HIPAA), or the Payment Card Industry Data Security Standard (PCI DSS), and ensure your data security practices align with them.
Visit: highlights of data protection bill
In conclusion, data security is a paramount concern in today’s digital landscape. Implementing these top 10 data security best practices can significantly reduce the risk of data breaches, protect your sensitive information, and safeguard your organization’s reputation. Remember that data security is an ongoing process that requires continuous monitoring, adaptation to new threats, and a commitment to maintaining the highest standards of protection. By following these top data security practices, you can fortify your defenses and keep your data safe in an increasingly interconnected world.

